SPARK Matrix: Leading Governance, Risk & Compliance (GRC) Platforms Driving Business Resilience
In today’s digital world, businesses face growing risks from cyber threats, regulatory changes, and operational challenges. To manage these complexities, organizations are adopting Governance, Risk, and Compliance (GRC) platforms. The latest SPARK Matrix™: GRC Platforms, Q2 2025 by QKS Group provides a detailed analysis of this evolving market and highlights the leading technology vendors.
What is a GRC Platform?
A GRC platform is a centralized software solution that helps organizations manage governance, risk, and compliance activities in an integrated way. These platforms provide tools to identify risks, ensure regulatory compliance, and improve decision-making across business functions.
Modern GRC solutions typically include modules for:
Risk management
Compliance tracking
Policy management
Audit management
Vendor risk management
By bringing all these capabilities into a single system, organizations can reduce manual work, improve visibility, and respond quickly to risks.
About the SPARK Matrix™
The SPARK Matrix™ is a well-known evaluation framework that analyzes and ranks vendors based on two key parameters:
• Technology Excellence
• Customer Impact
It provides a competitive comparison of leading vendors and helps businesses understand market trends, vendor strengths, and strategic positioning.
The Q2 2025 report offers deep insights into global market dynamics, emerging technologies, and vendor innovation in the GRC space.
Key Trends in the GRC Market
The report highlights several important trends shaping the future of Governance, Risk, and Compliance platforms:
1. Integration and Centralization
Organizations are moving away from siloed tools toward unified platforms. A centralized GRC system improves collaboration across departments and ensures consistent risk management practices.
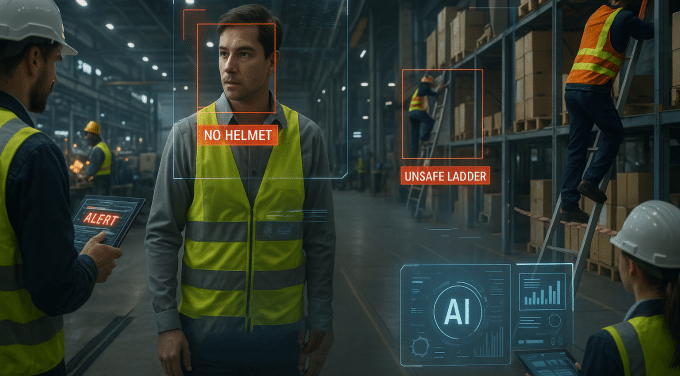
2. Automation and AI Adoption
Automation is becoming a core feature in GRC platforms. AI-driven analytics help in identifying risks early, predicting threats, and improving compliance monitoring.
3. Focus on Real-Time Risk Visibility
Businesses now demand real-time dashboards and continuous monitoring capabilities. This helps in faster decision-making and proactive risk mitigation.
4. Regulatory Complexity
With increasing global regulations, companies need flexible platforms that can adapt to different compliance requirements across regions and industries.
Vendor Landscape and Competition
The SPARK Matrix™ evaluates multiple global vendors and ranks them based on their capabilities. Vendors are categorized into leaders, challengers, and emerging players.
For example, companies like Swiss GRC have been recognized as leaders due to their strong technology capabilities and customer-centric solutions.
Leading vendors stand out by offering:
Scalable and modular platforms
Strong integration capabilities
Advanced analytics and reporting
High customization and flexibility
These features enable organizations to align GRC processes with business goals effectively.
Why GRC Platforms are Important in 2025
In 2025, GRC platforms are no longer optional—they are essential. Businesses must deal with increasing cyber risks, data privacy regulations, and operational uncertainties.
A modern GRC platform helps organizations:
Reduce compliance risks
Improve operational efficiency
Strengthen governance frameworks
Enhance transparency and accountability
It also enables a proactive approach to risk management instead of reacting to issues after they occur.
Conclusion
The SPARK Matrix™: Governance, Risk, and Compliance Platforms, Q2 2025 by QKS Group provides valuable insights into the current state of the GRC market. It highlights how technology innovation, automation, and integration are transforming the way organizations manage risk and compliance.
As businesses continue to evolve, adopting a robust GRC platform will be critical for staying compliant, secure, and competitive. Organizations that invest in advanced GRC solutions today will be better prepared to handle future challenges and achieve long-term success
#GRC #RiskManagement #Compliance #Governance #CyberSecurity #AI #GRC #GovernanceRiskCompliance #GRCPlatform #GRCSoftware #RiskManagement #Compliance #RegTech #AIinGRC #GRC #GovernanceRiskCompliance #GRCPlatform #GRCSoftware #RiskManagement #ComplianceManagement #Riskmanagement #AIinGRC #GRCMarket #RiskAnalytics #CyberRisk
In today’s digital world, businesses face growing risks from cyber threats, regulatory changes, and operational challenges. To manage these complexities, organizations are adopting Governance, Risk, and Compliance (GRC) platforms. The latest SPARK Matrix™: GRC Platforms, Q2 2025 by QKS Group provides a detailed analysis of this evolving market and highlights the leading technology vendors.
What is a GRC Platform?
A GRC platform is a centralized software solution that helps organizations manage governance, risk, and compliance activities in an integrated way. These platforms provide tools to identify risks, ensure regulatory compliance, and improve decision-making across business functions.
Modern GRC solutions typically include modules for:
Risk management
Compliance tracking
Policy management
Audit management
Vendor risk management
By bringing all these capabilities into a single system, organizations can reduce manual work, improve visibility, and respond quickly to risks.
About the SPARK Matrix™
The SPARK Matrix™ is a well-known evaluation framework that analyzes and ranks vendors based on two key parameters:
• Technology Excellence
• Customer Impact
It provides a competitive comparison of leading vendors and helps businesses understand market trends, vendor strengths, and strategic positioning.
The Q2 2025 report offers deep insights into global market dynamics, emerging technologies, and vendor innovation in the GRC space.
Key Trends in the GRC Market
The report highlights several important trends shaping the future of Governance, Risk, and Compliance platforms:
1. Integration and Centralization
Organizations are moving away from siloed tools toward unified platforms. A centralized GRC system improves collaboration across departments and ensures consistent risk management practices.
2. Automation and AI Adoption
Automation is becoming a core feature in GRC platforms. AI-driven analytics help in identifying risks early, predicting threats, and improving compliance monitoring.
3. Focus on Real-Time Risk Visibility
Businesses now demand real-time dashboards and continuous monitoring capabilities. This helps in faster decision-making and proactive risk mitigation.
4. Regulatory Complexity
With increasing global regulations, companies need flexible platforms that can adapt to different compliance requirements across regions and industries.
Vendor Landscape and Competition
The SPARK Matrix™ evaluates multiple global vendors and ranks them based on their capabilities. Vendors are categorized into leaders, challengers, and emerging players.
For example, companies like Swiss GRC have been recognized as leaders due to their strong technology capabilities and customer-centric solutions.
Leading vendors stand out by offering:
Scalable and modular platforms
Strong integration capabilities
Advanced analytics and reporting
High customization and flexibility
These features enable organizations to align GRC processes with business goals effectively.
Why GRC Platforms are Important in 2025
In 2025, GRC platforms are no longer optional—they are essential. Businesses must deal with increasing cyber risks, data privacy regulations, and operational uncertainties.
A modern GRC platform helps organizations:
Reduce compliance risks
Improve operational efficiency
Strengthen governance frameworks
Enhance transparency and accountability
It also enables a proactive approach to risk management instead of reacting to issues after they occur.
Conclusion
The SPARK Matrix™: Governance, Risk, and Compliance Platforms, Q2 2025 by QKS Group provides valuable insights into the current state of the GRC market. It highlights how technology innovation, automation, and integration are transforming the way organizations manage risk and compliance.
As businesses continue to evolve, adopting a robust GRC platform will be critical for staying compliant, secure, and competitive. Organizations that invest in advanced GRC solutions today will be better prepared to handle future challenges and achieve long-term success
#GRC #RiskManagement #Compliance #Governance #CyberSecurity #AI #GRC #GovernanceRiskCompliance #GRCPlatform #GRCSoftware #RiskManagement #Compliance #RegTech #AIinGRC #GRC #GovernanceRiskCompliance #GRCPlatform #GRCSoftware #RiskManagement #ComplianceManagement #Riskmanagement #AIinGRC #GRCMarket #RiskAnalytics #CyberRisk
SPARK Matrix: Leading Governance, Risk & Compliance (GRC) Platforms Driving Business Resilience
In today’s digital world, businesses face growing risks from cyber threats, regulatory changes, and operational challenges. To manage these complexities, organizations are adopting Governance, Risk, and Compliance (GRC) platforms. The latest SPARK Matrix™: GRC Platforms, Q2 2025 by QKS Group provides a detailed analysis of this evolving market and highlights the leading technology vendors.
What is a GRC Platform?
A GRC platform is a centralized software solution that helps organizations manage governance, risk, and compliance activities in an integrated way. These platforms provide tools to identify risks, ensure regulatory compliance, and improve decision-making across business functions.
Modern GRC solutions typically include modules for:
Risk management
Compliance tracking
Policy management
Audit management
Vendor risk management
By bringing all these capabilities into a single system, organizations can reduce manual work, improve visibility, and respond quickly to risks.
About the SPARK Matrix™
The SPARK Matrix™ is a well-known evaluation framework that analyzes and ranks vendors based on two key parameters:
• Technology Excellence
• Customer Impact
It provides a competitive comparison of leading vendors and helps businesses understand market trends, vendor strengths, and strategic positioning.
The Q2 2025 report offers deep insights into global market dynamics, emerging technologies, and vendor innovation in the GRC space.
Key Trends in the GRC Market
The report highlights several important trends shaping the future of Governance, Risk, and Compliance platforms:
1. Integration and Centralization
Organizations are moving away from siloed tools toward unified platforms. A centralized GRC system improves collaboration across departments and ensures consistent risk management practices.
2. Automation and AI Adoption
Automation is becoming a core feature in GRC platforms. AI-driven analytics help in identifying risks early, predicting threats, and improving compliance monitoring.
3. Focus on Real-Time Risk Visibility
Businesses now demand real-time dashboards and continuous monitoring capabilities. This helps in faster decision-making and proactive risk mitigation.
4. Regulatory Complexity
With increasing global regulations, companies need flexible platforms that can adapt to different compliance requirements across regions and industries.
Vendor Landscape and Competition
The SPARK Matrix™ evaluates multiple global vendors and ranks them based on their capabilities. Vendors are categorized into leaders, challengers, and emerging players.
For example, companies like Swiss GRC have been recognized as leaders due to their strong technology capabilities and customer-centric solutions.
Leading vendors stand out by offering:
Scalable and modular platforms
Strong integration capabilities
Advanced analytics and reporting
High customization and flexibility
These features enable organizations to align GRC processes with business goals effectively.
Why GRC Platforms are Important in 2025
In 2025, GRC platforms are no longer optional—they are essential. Businesses must deal with increasing cyber risks, data privacy regulations, and operational uncertainties.
A modern GRC platform helps organizations:
Reduce compliance risks
Improve operational efficiency
Strengthen governance frameworks
Enhance transparency and accountability
It also enables a proactive approach to risk management instead of reacting to issues after they occur.
Conclusion
The SPARK Matrix™: Governance, Risk, and Compliance Platforms, Q2 2025 by QKS Group provides valuable insights into the current state of the GRC market. It highlights how technology innovation, automation, and integration are transforming the way organizations manage risk and compliance.
As businesses continue to evolve, adopting a robust GRC platform will be critical for staying compliant, secure, and competitive. Organizations that invest in advanced GRC solutions today will be better prepared to handle future challenges and achieve long-term success
#GRC #RiskManagement #Compliance #Governance #CyberSecurity #AI #GRC #GovernanceRiskCompliance #GRCPlatform #GRCSoftware #RiskManagement #Compliance #RegTech #AIinGRC #GRC #GovernanceRiskCompliance #GRCPlatform #GRCSoftware #RiskManagement #ComplianceManagement #Riskmanagement #AIinGRC #GRCMarket #RiskAnalytics #CyberRisk
0 Commenti
0 condivisioni
49 Views





.png)